Overwrite Existing File Vulnerabilities | Tryhackme
Basic file-upload vulnerabilities in websites parte 1
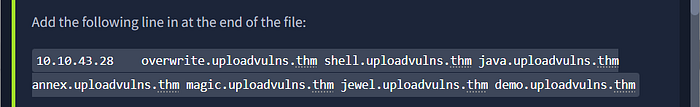
To make your virtual host (VHOST) accessible, you’ll need to modify your system’s hosts file.
sudo nano /etc/hostsAdd the following entry to your hosts file (replace MACHINE_IP with the IP address provided by TryHackMe.

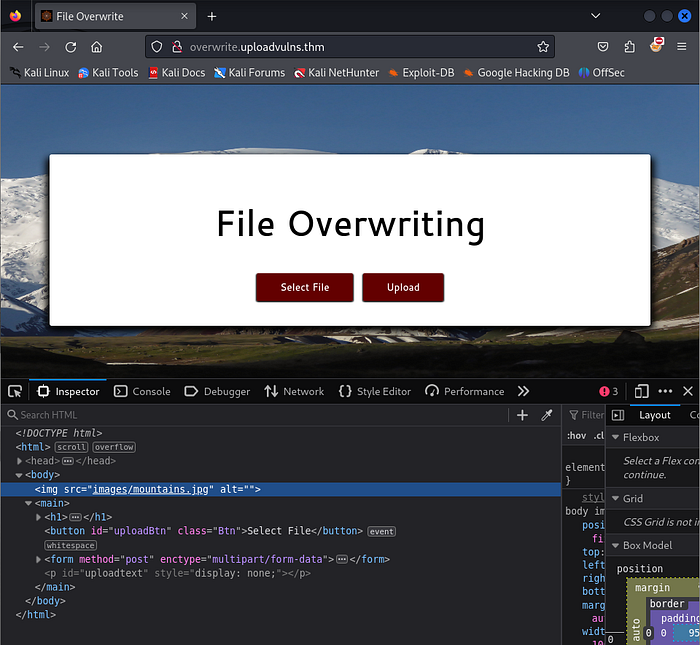
And then, we able to access the website.
TASKS
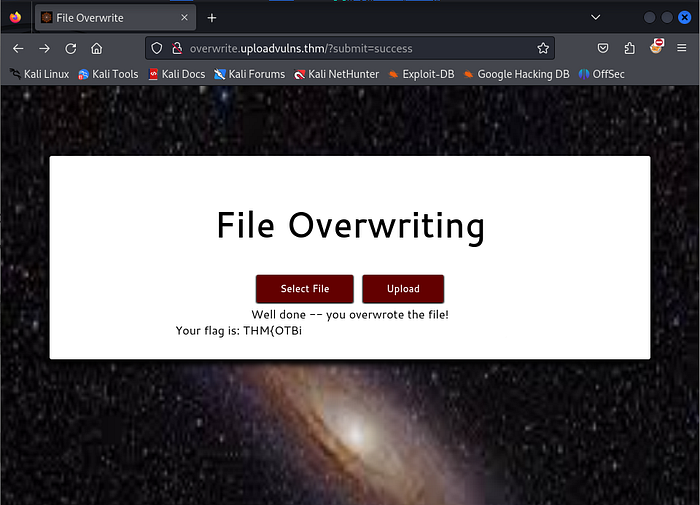
Open your web browser and navigate to overwrite.uploadvulns.thm. Your goal is to overwrite a file on the server with an upload of your own.
Let’s Do It
In the tutorial, they show how the attack works. By inspecting the URL of the image, we can see that mountains.jpg is displayed as the background. We can do the same, we just need to find a picture, download it, and rename it to mountains.jpg .
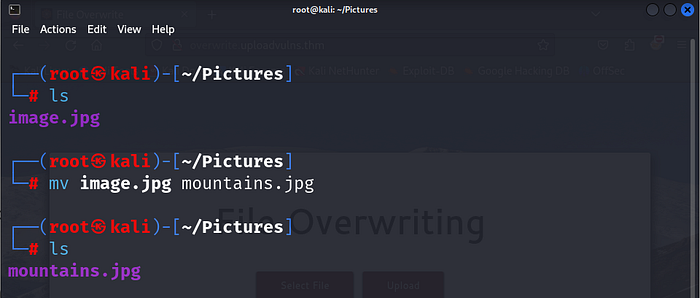
After renaming the image file, we can upload it, and voilaaa, we got the flag ⛳.
How To Prevent It
When uploading files to a server, it’s important to prevent overwriting existing files. Here’s how servers typically handle this:
- Renaming Files — The server may give the file a new name (e.g., adding random characters or a timestamp).
- Filename Checks — If a file with the same name already exists, the server can reject it and ask the user to pick a different name.
- File Permissions — Critical files (like web pages) should have restricted write access to stop attackers from overwriting them.
Thank you for reading this until the end! This write-up serves as my personal journal while working through this room, documenting my journey, challenges, and learnings along the way. I hope it can also be a helpful resource for others exploring similar paths.









